Identity Management
5 Key Reasons for Adopting a Centralized Identity Management System
1) User Management System (CIAM)
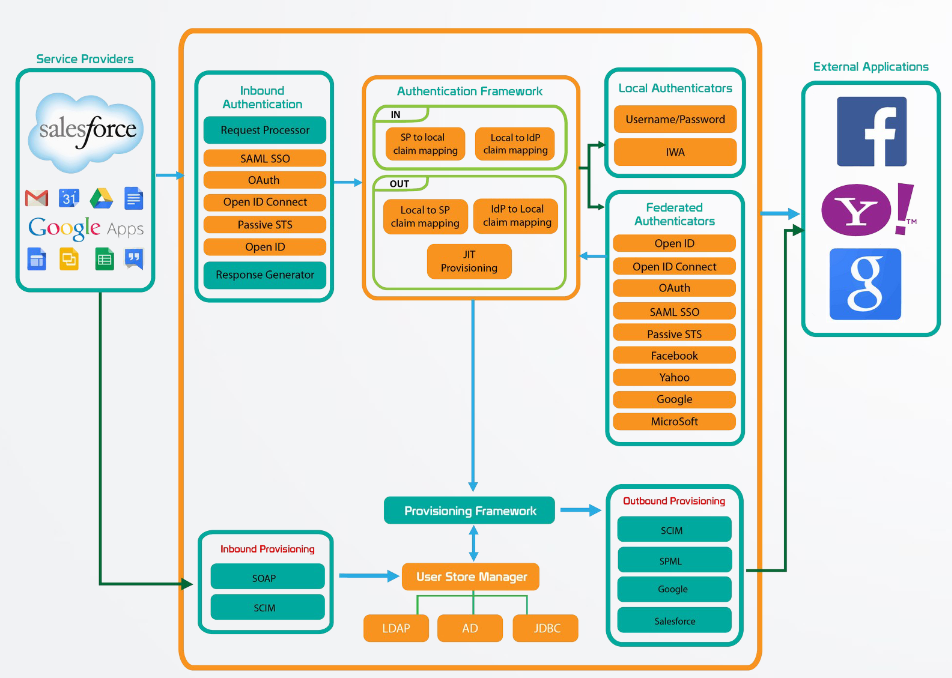
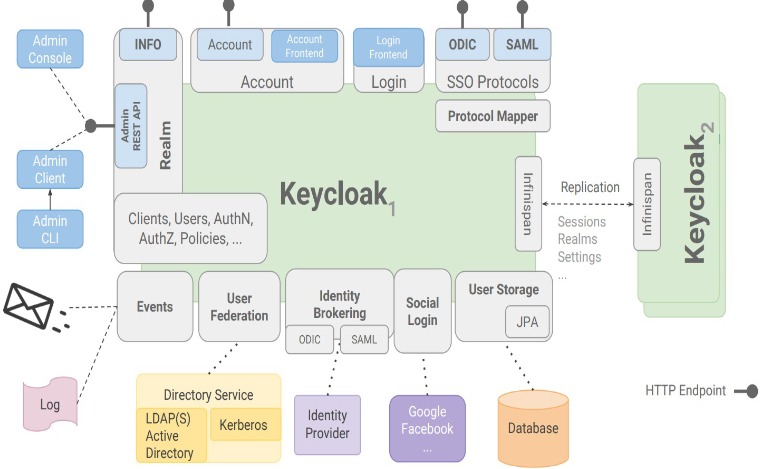
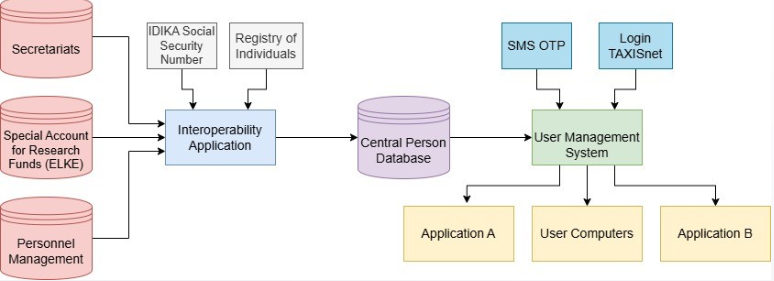
Consolidation of all users into a single management point. A CIAM allows us to create a unified repository or integrate all existing users. It enables easier and more secure user management, simplifies password management, and supports repositories like LDAP, Active Directory, or other databases.
2) Security
Consolidating all users into a specialized security-focused point with modern security mechanisms reduces security breaches. Multifactor authentication (SMS, email OTP) and adaptive authentication (based on IP, device) enhance security for all applications.
3) Support for Multiple Identity Providers
A modern CIAM supports external Identity Providers such as Social Authenticators (Facebook, Google, OAuth2) and institutional providers (Taxisnet Login, Shibboleth, eIDAS nodes). Users can select preferred IdPs per application.
4) Integration of All Applications into a Common Point
An Identity server supports OAuth2, SAML2 for web/mobile applications, and REST APIs for legacy desktop apps. These technologies ensure the security of IoT devices as well.
5) Compliance with Standards and Regulatory Frameworks
Built-in support for GDPR (user consent management, user dashboards), PSD2, and eIDAS ensures compliance with industry regulations, improving overall security and user data management.



 Home
Home